SecEng Newsletter #3

Welcome to Issue #3 of the Security Engineering Newsletter.
I have some exciting news to share next week that was a direct result of starting this newsletter. 🥳
-- Andrew

post by me! I went into some detail on how to run scheduled scripts on your Mac using Launch Agents. Launch Agents are super common among Mac malware for maintaining persistence, so it might be a good refresher to check this post to get a brief understanding on how they work if you have Macs in your work environment.
Building Secure and Reliable Systems by Google is an essential security engineering read and is free to read on Google's GitHub site. Compared to the Ross Anderson book I posted last week, this book is a walk in the park but still incredibly helpful and insightful regardless.
deptry is a command line tool to check for issues with dependencies in a Python project, such as unused or missing dependencies.
I haven't tried this tool yet, but it is something that I have always wanted. I think it is pretty easy for orphaned dependencies to hang around in a project for a while, increasing attack surface and such. deptry seems like it would be great addition to CICD pipelines or just doing some checks on a few projects to trim them down.

The premise of this post is that you should keep a WTF Notebook after joining a team. Any time you see something that makes you say WTF, add it to the notebook, but don't make a huge fuss (within reason) yet . Once you have more context about the environment and its problems, you prioritize which WTFs to work on first.

Ruff is an extremely fast Python linter and code formatter, written in Rust.
I love this quote in their docs from Sebastián Ramírez, creator of FastAPI:
Ruff is so fast that sometimes I add an intentional bug in the code just to confirm it's actually running and checking the code.
This is another one that I want to try, but haven't gotten around to yet 🗡️

Not only do I agree with the sentiment of this article, but I found that it had some good tips about working with JSON in general.
TLDR points:
- Always think of the end-user and how they will interact with the data.
- Do Make a Schema
- Do Flatten the Structure
- Do Use Predictable Key Names
- Do Pretty Print with Two Spaces or Don’t Format at All
- Don’t Use Special Characters in Key Names
- Don’t Allow Duplicate Keys
- Don’t Use Very Large Numbers
At first glance you may think this appears to be your average cringey, clickbait YouTube video selling a course on AI, but you would be very wrong, friend. Mike Pound is an absolute legend and I will never pass up a chance to watch him talk about computers.


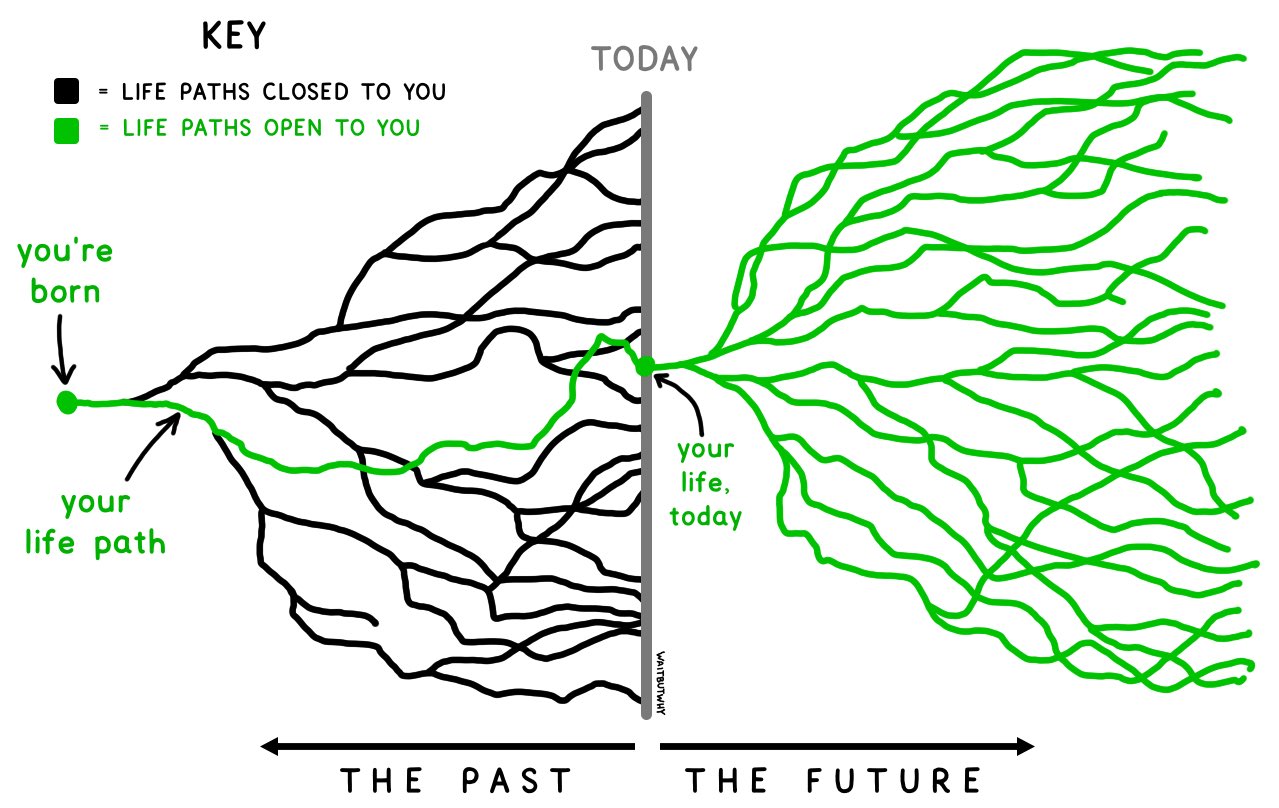
I saw this post on HN randomly and I thought it was extremely well written and thought-provoking. I love the part about becoming a new person every 3-6 years. For most people, I think this rate of change is pretty much inevitable and you just have to roll with it and embrace it.

Congratulations to Sublime Security (email security using AI and a transparent detection engine) for raising $20M in Series A Funding!

Congratulations to Tines (security automation/SOAR) for raising an additional $50M in Series B Funding!
It is fantastic to see the continued success of these two companies. I highly recommend giving them a look if you haven't yet. Both of these products embody what I value most in security tooling:
- it allows me to do far less work
- it does what it says on the tin
- it allows you to be extremely creative
The fact that I am just posting this of my own volition without any incentive should speak volumes to how great these products are. Keep up the f***ing amazing work.


.png?1666990288)

Thank you for reading this week's issue, and see you next week! If you have any feedback, hit me up!







Discussion