SecEng Newsletter #2

Welcome to Issue #2 of the Security Engineering Newsletter.
If you or someone you know has a SecEng blog, please send it to me at andrew@akatz.org! I need more stuff to read!
I am currently reading The Art of Mac Malware by Patrick Wardle and just want to say... this book is DAMN incredible. If you want to beef up your Mac security and internals knowledge and learn about malware, I strongly recommend it. If you are feeling uninspired, it's reading stuff like this that can get you going again.
To any of the 20+ people who subscribed so far, my sincere thanks! I was absolutely chuffed to see some familiar people subscribe and I feel pumped to write and share on this platform. As a token of my gratitude, here is a picture of my cat Mogwai.
-- Andrew
Ross Anderson passed away. Ross's book on Security Engineering (https://www.cl.cam.ac.uk/~rja14/book.html) is unmatched and has been pivotal in building my career. I would recommend at least reading chapter 3, "Who is the opponent" because it may rightly scare the shit out of you. He has also posted video lectures of his security engineering course at University of Cambridge on YouTube. He will be missed.

I wrote a post about what I think is the prototypical Python example in security engineering. This is followed by a short tangent on leetcode (YAY!) in SecEng interviews and how to get started in Python.
Tracecat 😼 positions itself as an open source alternative to paid SOAR platforms. It looks like they are working hard to deliver on some core features this year. Reading through their docs, it seems they have their head on straight about AI features as well. I'm excited to check on it again to see how things look in a year or two.
Thoughts 🤔
- How much will it cost to run this in AWS if you are a team that has a ton of playbooks and absolutely hammers their SOAR with events 24/7 (like some people I know)?
- Will Tracecat be able to handle my crazy mad scientist playbooks with 30 webhooks and 1200 actions?
Asking the important questions here.
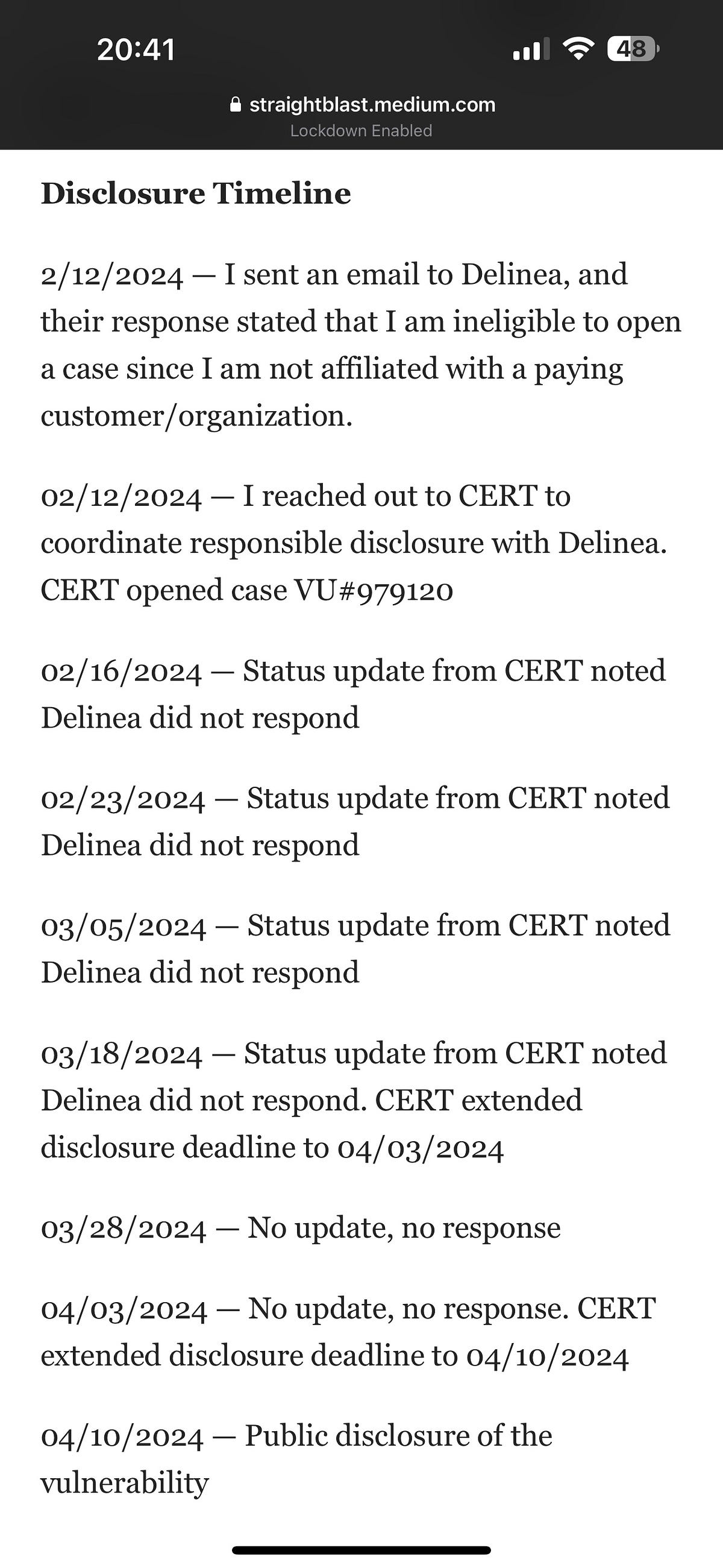
Kevin Beaumont has a write-up about an authorization bypass vulnerability in Delinea/Thycotic Secret Server and how the company seemed to have fumbled in the disclosure process.
Delinea say they believe no customer data was impacted. If you want to search your own Secret Server instance, Delinea has posted some SQL queries that you can create a report and search for IOCs with: https://support.delinea.com/s/article/KB-010572-How-do-I-remediate-Secret-Server-in-reference-to-the-Secret-Server-SOAP-vulnerability

Previously reserved for government organizations at the federal, state, local, tribal, and territorial levels, CISA's Malware Next-Gen now allows submissions from any person or organization in the country. But... you have to use a typical, terrible government form...and they won't tell you the results of your submission unless you register. Maybe I am being too harsh, but I am finding it difficult to be excited about this.
Random cool thing: Did you know you can run DynamoDB as a Docker container? Pretty nice for developing locally before creating resources in AWS.
NSA published a guide on strengthening AI system security. Somewhat unsurprisingly, sound practices and requirements for IT environments apply to AI systems too, although there is a significant amount of AI-specific information here that is worth the read. Prompt injection attacks, protecting model weights, red teaming, rolling back models, and so on...
Side note: AI red teaming sounds like a really interesting job.
Johan Berggren and Matt Linton's talk from Black Hat Europe 2023 discusses burnout on security teams. How can we make sure that we are able to recognize these signs in ourselves and others? They submit that there are two types of burnout: situational and chronic. Situational tends to be a fast onset thing that surfaces when working an extremely difficult incident while chronic occurs over a long period of time.
I would say there are definitely multiple levels of burnout. There is the low-to-mid-level burnout where you are overworking yourself, possibly not going outside for days, and easily irritated. And then there is the earth-shattering burnout I have only read about where you pretty much cannot bring yourself to work for 9+ months.



For those of us working with AI, LLMs, etc., be sure to check this one out. This post by Ken Kantzer has some knowledge-bomb-level takeaways on prompt engineering. I was surprised that NOT enumerating an exact list or instructions in the prompt produced better results. I was not surprised, however, by this line:
"Return nothing if you don’t find anything” – is probably the most error-prone prompting language we came across. Not only does GPT often choose to hallucinate rather than return nothing, it also causes it to just lack confidence a lot, returning blank more often than it should."

🚨 Cat saves company thousands of dollars in AWS expenditure by waking up owner to fend off DDoS attack. My cat just wakes me up at 4 am for no reason.
Jeff McJunkin on bypassing AV on Windows. This is old (2020), but still great, and I was reminded of it today and wanted to share it.

.png?1673531443)


.jpg?1664319254)
Thank you for reading this week's issue, and see you next week! If you have any feedback, hit me up!







Discussion